Code Quality Taxonomy Updates
In SonarQube Server 10.3, Sonar is releasing further updates based on the Code Quality Taxonomy to support our commitment to Code Quality. Focusing on the consequences of poorly written or bad code is complicated and leads to confusion. More often than not, problems with code can have multiple or overlapping consequences. Instead, Sonar turns your attention to what causes bad code and helps you prevent it. Code Quality that is consistent, intentional, adaptable, and responsible prevents code from being poorly constructed. Sonar’s Code Quality Taxonomy is a framework that brings together our most current technology to make your code the best it can be.
Simplified Code Quality Attribute in Pull Requests for all CI Platforms
To clearly explain why your code has quality issues, the PR In-product Summary and PR Decoration now show a single “issues” condition per the Code Quality Taxonomy. Prior to this release, issues in the Pull Request’s In-product Summary in SonarQube Server and Pull Request Decoration in each Continuous Integration (CI) platform were listed under the results-driven categories of “reliability”, “security”, and “maintainability”. This change is supported in all CI platforms: GitHub, GitLab, Bitbucket, and Azure DevOps.
External Issues Fully Leverage Code Quality Taxonomy Characteristics
In the 10.3 release, external issues can be categorized with the new Code Quality Taxonomy in the same way as issues raised natively by Sonar. Previously, external issues were classified only using the original categorization, and it was difficult to understand how the external issues fit within the new classification.
Updates to Code Quality Taxonomy Rules are Applied to All Projects and All Issues
Quality Profiles have been updated with the new Code Quality Taxonomy characteristics. Now, as Sonar updates the new Code Quality Taxonomy, the corresponding updates to the rules released in support of those changes are automatically propagated to all issues in all projects, which can be applied to analyze historical code and not just newly written code. These changes together deliver the full benefit of the new taxonomy to you.
Exclude Inherited Rule From a Parent Quality Profile
When you inherit a Quality Profile the undesired rules can be selectively excluded from the parent Quality Profile. Prior to this change, SonarQube Server required you to use all the rules from the inherited parent profile. If one or more of the inherited rules were not relevant to the way your project was set up, the only solution was to copy the parent Quality Profile and remove the rules that weren’t needed. As a result of copying the Quality Profile, you would lose the benefit of inheritance. With this new change, the benefits of inheritance can be realized. You can now safely rely on the built-in “Sonar way” Quality Profiles by inheriting them and continue to get the latest and greatest changes from Sonar as we make updates without any work by you. For companies that do not want their teams to exclude any rules when inheriting, this feature can be disabled.
Clean as You Code Improvements
Fixing technical debt in legacy code is often a costly and high-risk effort that pulls resources from innovation. Sonar's solution eliminates this challenge by focusing your teams on new code.
By enabling developers to improve code quality as they write, all new code meets a high quality standard. This approach is the most effective way to prevent new technical debt from being introduced. As your teams build new capabilities, they naturally touch portions of legacy code. Over time, this means a growing percentage of that legacy code is also improved and remediated as a direct consequence of new development, systematically reducing your existing technical debt.
Sonar way Quality Gate Adopts Rigorous Clean as You Code Criteria
As a best practice, Sonar is moving to more exacting Clean as You Code criteria of allowing zero issues in the built-in Sonar way Quality Gate. By not following a strict zero issues policy as you write new code, a certain amount of technical debt is continually allowed into your code. Additionally, the Sonar way Quality Gate no longer individually shows bugs, vulnerabilities, and code smells. The new single category “issues” and the zero issues policy together represent SonarSource's recommended quality criteria for new code. These changes provide an even more robust framework that ensures newly written and modified code meets the highest possible Code Quality standards.
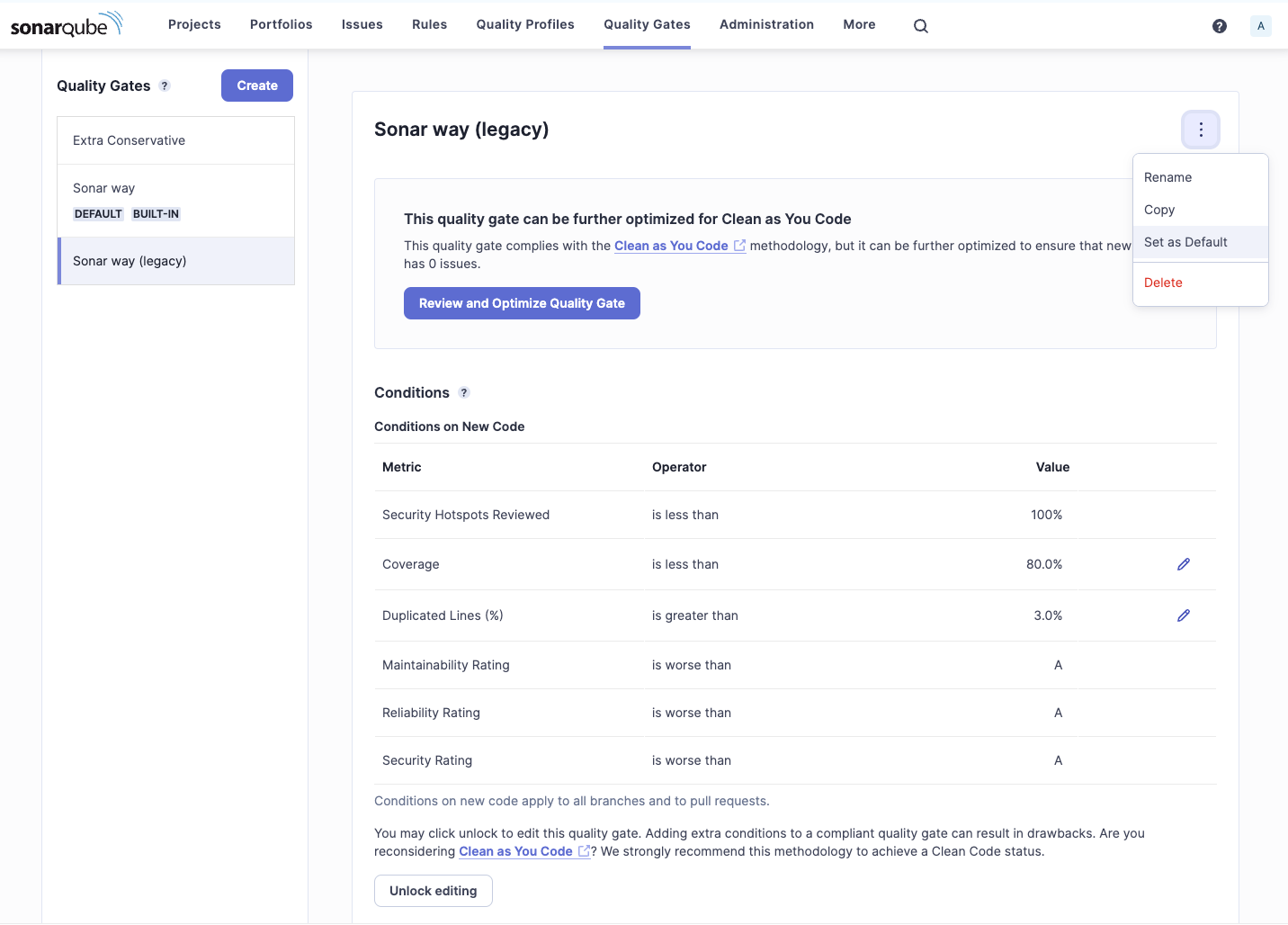
Both the new Built-in Sonar way Quality Gate and the legacy Sonar way Quality Gate can be set as the default.
Learn more about our criteria for maintaining code standards and the new Sonar way Quality Gate.
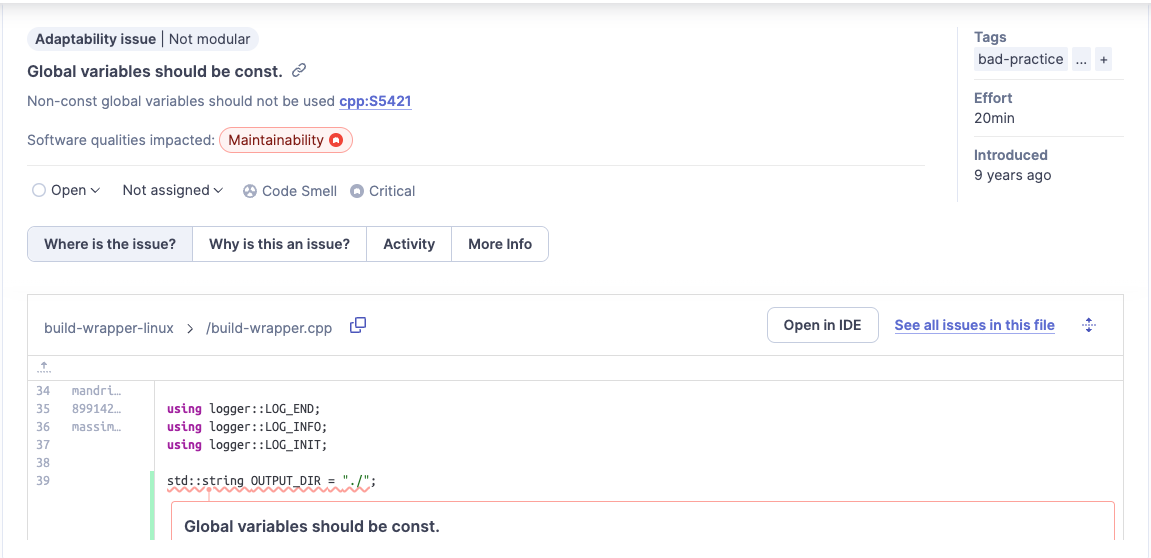
Open an Issue in your IDE
When in Connected Mode with SonarQube for IDE, as you work through issue resolution in SonarQube Server, you can quickly jump to the code in question to fix it within your IDE. All issues in SonarQube Server show a button that, when clicked, will open up SonarQube for IDE in your IDE and show you the code that is causing the issue.
Resolve External Issues in SonarQube Server
You can now resolve External Issues inside SonarQube Server in the same place as issues raised by SonarQube Server instead of leaving SonarQube Server to swivel-chair to the source of the external issue to dismiss it.
Stronger SonarQube Server Security Capabilities
With the SonarQube Server 10.3 release, Sonar continues to strengthen its position on security so that your code is better than ever. One of the most severe security breaches is illicit access to a company’s private data, especially the data of employees or customers. Sonar now has our most thorough secrets detection capability to prevent secrets from entering your CI/CD pipeline and leaking out to the public. We have added the new 2023 CWE Top 25 Report for you to assess risk against. SonarQube Server now stays in sync with the GitLab Vulnerability Report, so you don’t have to switch back to GitLab to check on any issues’ status changes. Together with several other enhanced security capabilities detailed below, you will get Sonar’s most advanced tooling for ensuring your code is high-quality and clear of security issues.
Secrets Detection at the Source
Sonar’s new secrets detection engine helps you keep secrets out of your code while you develop in your IDE with SonarQube for IDE. Unlike other tools that only scan your repository, we eliminate those secrets in a true shift left approach at the source, and with SonarQube Server we further protect secrets from entering into your CI/CD pipeline. Sonar detects the top 100+ common patterns that contain the most sensitive secrets/tokens. For companies that want to protect against leaks of secrets unique to your company, in the Enterprise Edition and Data Center Edition, you can create your own custom rules to detect company-specific secrets.
See Sonar's Secrets Documentation.
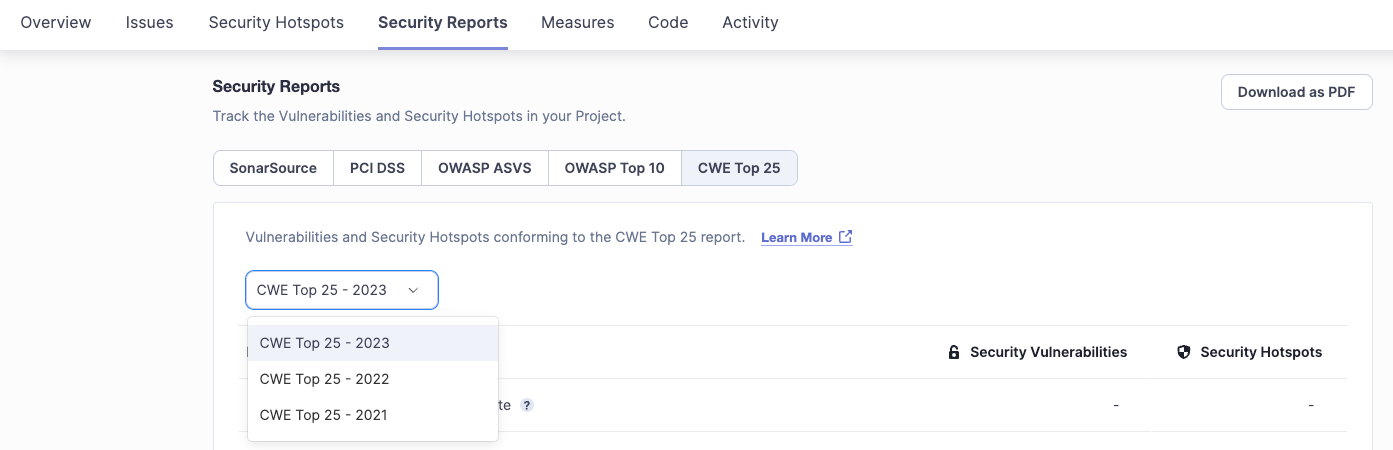
Assess Risk Against the 2023 CWE Top 25 Report
The Security Reports page in SonarQube Server now contains the CWE Top 25 2023 Report for use when assessing your risk against it. As of the 10.3 release, the Security Reports page has data from the 2023, 2022, and 2021 CWE Top 25 Reports.
GitLab Vulnerability Report Issues Status is Propagated Back to SonarQube Server
In the 10.2 release, Sonar added the capability to synchronize issues back to the GitLab Vulnerability Report when SonarQube Server detected an issue or updated the status of an issue. With this update, status changes of issues in the GitLab Vulnerability Report are automatically replicated back to the corresponding issue in SonarQube Server in the subsequent analysis, eliminating any discrepancy between the two systems. This completes a two-way auto-synchronization of issue statuses between Sonar and the GitLab Vulnerability Report.
Enhanced Support for Dockerfiles
Sonar helps you create clear and consistent Dockerfiles by adding more rules for Dockerfiles. Support for Dockerfiles now includes security and other attributes of Code Quality with the addition of more than 20 new rules.
Top Security Issue Requests
The top security enhancement requests are included in the SonarQube Server 10.3 release.
- Alias tracking is improved during branching to prevent the loss of an alias.
- PHP code taint analysis is improved by supporting global variables.
- All comparison operators in Java, JavaScript, Python, and C# are considered as validators.
New Data Science Libraries Supported in Python
Are you a Data Scientist or Machine Learning Practitioner? If so, Sonar has excellent news for you. We’ve taken a big step towards supporting the top Python libraries you use. Sonar already offers support for Jupyter Notebooks in VS Code, and we’re very excited to announce that we’ve released new rules to support the NumPy and Pandas Python libraries. Please watch future releases as we expand support for more DS/MLp Python libraries.
Easy Onboarding
Provision GitHub projects with ease and flexibility
When you use GitHub Action to create and configure your GitHub project, SonarQube Server can handle it. Gone are the days of manually making changes between GitHub and SonarQube Server to ensure they are configured the same.
You can:
- Automatically create and configure a SonarQube Server project when an analysis is triggered from GitHub, including auto-population of:
- PR decoration (Developer Edition+ only)
- Main branch name
- Fully automate SonarQube Server project setup via API
- Sync Teams Between GitHub and SonarQube Server
For companies with more complex project permissions, you can configure SonarQube Server to overwrite the default SonarQube Server permissions mapping and auto-sync users, permissions, and groups from GitHub. You no longer need to manually configure users, permissions, and groups in SonarQube Server and ensure they are correctly aligned with those in GitHub.
Support for Blazor Framework
Sonar has added support for the Blazor front-end web framework for building interactive client-side web UI in .NET. By leveraging .NET, C#, HTML, Razor templates, and SonarQube Server together, you can build full-stack web apps that contain Code Quality. With the addition of support for Blazor in SonarQube Server, you can now analyze .cshtml and .razor files for building front-end apps and C# for back-end applications in .NET projects. This highly requested feature will help you keep your ASP.NET Core MVC, Razor, and Blazor applications clean.
SonarQube Server 10.3 Operational Improvements
Upgrade Change Messaging
After you upgrade to the new version and new rules are applied with a new analysis, there will likely be changes to your analysis results. To help you clearly understand the impact, the details of each change appear in the Activity Stream to explain what happened as a result of the upgrade.
UI Updates
Sonar is working to bring a modern experience to all our properties. In each release, we will continue to update pages with the new UI.
The following have been updated to the latest UI in the 10.3 release:
- Quality Gate page
- Rules page
- Quality Profiles page
- DevOps platform configuration modal visible during project onboarding
Language Updates
JavaScript/TypeScript:
- First-class support of React with more than 60 rules, including:
- Prevent common bad practices (17 new rules)
- Identify deprecated APIs (5 new rules)
- Improve accessibility (20 new rules)
- Improved diagnostics of memory issues
Java/Kotlin:
- Support of Maven 4.0
- Refresh of all external linters analyzers to get their latest rules
- Added support for Jakarta namespace
- Added Spring Boot most common pitfalls
C/C++
- Addition of new MISRA C++ 2023 rules
.NET
- Support of LTS .NET 8 and C#12
- Added support for C# code in .NET templates with Razor syntax, which can be used in ASP .NET and Blazor apps
Python:
- Support for Python 3.12 new syntax, new rules, and error-free parsing
- Addition of rules for top libraries used by Data Scientists
- NumPy
- Pandas