
Faster first analysis
Building on the LTS, we’ve further sped up the first full analysis of your git-based projects. With optimizations to the way git-blame data is collected and handled for all project files in the repository, the first project analysis is significantly faster.
In SonarQube Server 9.9 LTS, we made huge strides to speed up first analysis of git-based projects (avg 60-90% faster). In certain cases where the first analysis was relatively slower, we made further optimizations. Particularly projects that involve large volume of commits can now expect to see a much amplified improvement. For the two benchmark projects selected, we were able to see considerable speed up. The first full analysis on TypeScript compiler (~34K commits since it’s creation) that took more than 20 hours previously was completed is about 5 min with the improvements. Similarly, first analysis for TensorFlow, a popular ML framework, completed in less than 5 min as opposed to ~46 min in previous SQ versions including LTS.
Improved user management; new CWE security risk report
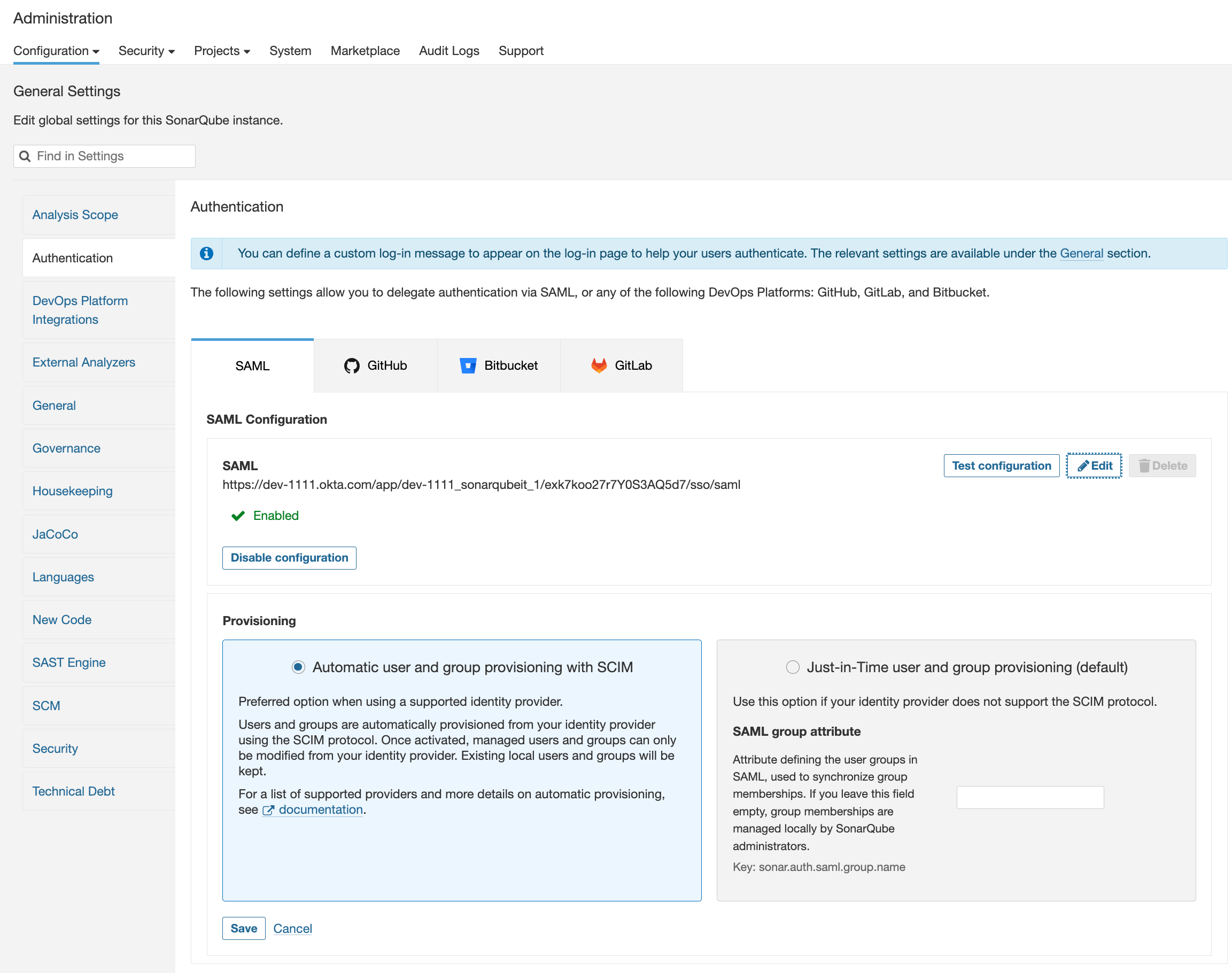
Admins will be pleased to note that user provisioning & deprovisioning now covers SAML/Azure AD – extending our support from SAML/Okta released earlier.
Admins no longer have to manually manage users and groups on SonarQube Server. SCIM integration automatically synchronizes user access from Azure AD to pre-provision user records or deactivate them & invalidate user tokens when a user leaves the organization. This ensures that user access always reflects what is applied in the identity provider(IdP), further strengthening security access from unauthorized users.
Building on that capability, group provisioning is also simpler for Okta and Azure AD. Admins can fully delegate user & group management to the IdP for secure and centralized provisioning for all their applications.
We’ve also added the CWE Top 25 2022 security risk report to help assess the risk of your codebase against commonly reported security vulnerabilities. To view this report, navigate to your project in SonarQube Server → Security Reports → CWE Top 25 where you can find the 2022, 2021, 2020 CWE reports.
Secure Dockerfiles for containerized app deployment
Dockerfiles can be an entry point for many security issues just like source code. We’ve added support for bash command parsing and over 20+ best practice rules to weed out any security misconfigurations in your Dockerfiles for secure deployment. Some examples include checking for the use of ‘sudo’ command, rules to check base image version is pinned, safe permission are set for ‘chmod’ option in COPY/ADD, and many others.
Check out all Docker documentation.
Language Updates
C/C++
- Support for clang-cl and Microchip compilers
C#, VB.NET
- 12 new best practice rules to deliver higher-quality .NET applications. Examples include checks to ensure ‘DebuggerDisplayAttribute’ are referring existing members to avoid debugging difficulties, new rules to identify empty C# blocks, correct declaration of “private” methods in classes, invalid mathematical comparisons, and more.
JS
- More advanced support for JavaScript built-ins with 8 new rules and 14 improved rules.