TL;DR overview
- Hexacon 2023 featured SonarSource vulnerability research presentations covering critical security findings in widely used open-source software and development tools.
- Sonar researchers presented technical details on newly discovered vulnerabilities, demonstrating attack chains that combine low-severity issues into high-impact exploits.
- The conference highlighted the importance of ongoing security research in the open-source ecosystem, where many projects lack dedicated security teams or formal threat modeling processes.
- SonarSource's participation reflects its commitment to improving ecosystem security through responsible disclosure and sharing technical knowledge with the broader security community.
Hexacon, now in its second iteration, stands as a premier IT security conference. Despite its relative youth, this event has quickly gained recognition as a prominent platform for cybersecurity professionals and enthusiasts. It serves as a hub for discussing highly technical content in the field of offensive IT security.
Participants have the opportunity to learn about the latest vulnerabilities and exploitation techniques, share knowledge, and network with like-minded individuals, making it a must-attend event for anyone passionate about IT security, like Sonar's AppSec Researchers and Vulnerability Researchers.
Hexacon 2023 - Venue and Events
The conference took place in the Palais Brongniart in Paris, France. With a historical significance dating back to its construction in 1808 instigated by Napoleon Bonaparte, this building is now one of the leading congress and event centers in Paris. This impressive building provided an opportune atmosphere for a highly professional conference like this.

The actual conference was preceded by four days of on-site training offering different topics such as Attacking the Linux Kernel, iOS for Security Engineers, or Practical Baseband Exploitation. For hands-on focused participants, the conference was enriched by three different challenges in the categories IoT, Web/Crypto, and RE/pwn. For those participants who were interested in networking, the social event of Friday evening provided a very pleasant opportunity to do so.
Hexacon 2023 - Talks
The single-tracked setup offered a variety of 15 different talks throughout the two days of the conference. Here are a few of our personal highlights:

Cheng-Da Tsai, aka Orange Tsai, invited the audience on an educational and entertaining journey of discovering and exploiting vulnerabilities in the Sonos One Speaker in the talk “A 3-Year Tale of Hacking a Pwn2Own Target: The Attacks, Vendor Evolution, and Lesson Learned”. Instead of focusing only on technical details, the talk outlined the general approach and highlighted the emotional ups and downs of vulnerability research.
The talk “Exploiting Hardened .NET Deserialization: New Exploitation Ideas and Abuse of Insecure Serialization” by Piotr Bazydło went beyond the usual exploitation strategies of deserialization vulnerabilities. Piotr emphasized the fundamental downsides of block lists by demonstrating different bypasses and even detailed bypass approaches applicable when allow lists are in place by leveraging nested deserialization. Furthermore, he showcased that even the re-serialization of objects can be leveraged by attackers. More details can be found in the related whitepaper.
Simon Scannell presented his impressive research on the Antivirus engine ClamAV in the talk “You have become the very thing you swore to destroy: Remotely exploiting an Antivirus engine”. Simon’s talk did not only explain the complex vulnerabilities he discovered in ClamAV but also detailed a unique exploit technique to bypass ASLR and eventually gain remote code execution.
The Hazards of Technological Variety and Parallelism: An Avocado Nightmare
On Friday, our Vulnerability Researcher Stefan Schiller presented the talk “The Hazards of Technological Variety and Parallelism: An Avocado Nightmare”, which highlighted two major challenges software is facing nowadays. The case study used for this purpose is Apache Guacamole, which is a remote desktop gateway commonly deployed in enterprise environments to access hosts and isolated applications via a web browser.
The talk described an interesting parser differential vulnerability caused by a difference in how Guacamole’s Java and C components handle Unicode characters and explained how attackers could exploit this. Furthermore, Stefan emphasized the dangers of parallelism by detailing a Use-After-Free vulnerability caused by the inappropriate protection of shared data access by separate threads. At last, he dived into the development of a proof-of-concept for this vulnerability and covered different glibc heap exploitation techniques in detail.
Thank you to everyone attending the talk and to the organizers for having us! We will publish an additional blog post covering the content of the talk soon. So, stay tuned!
Lightning Talks
Hexacon added a new format to the social event called Lighting Talks. A lightning talk is a quick session limited to 5 minutes, which should not contain any commercials but rather fun topics.
Our AppSec Researcher Gaëtan Ferry presented a tragically funny story about SAST engine benchmarking in his session “AppSeceo and Juliet C#”:
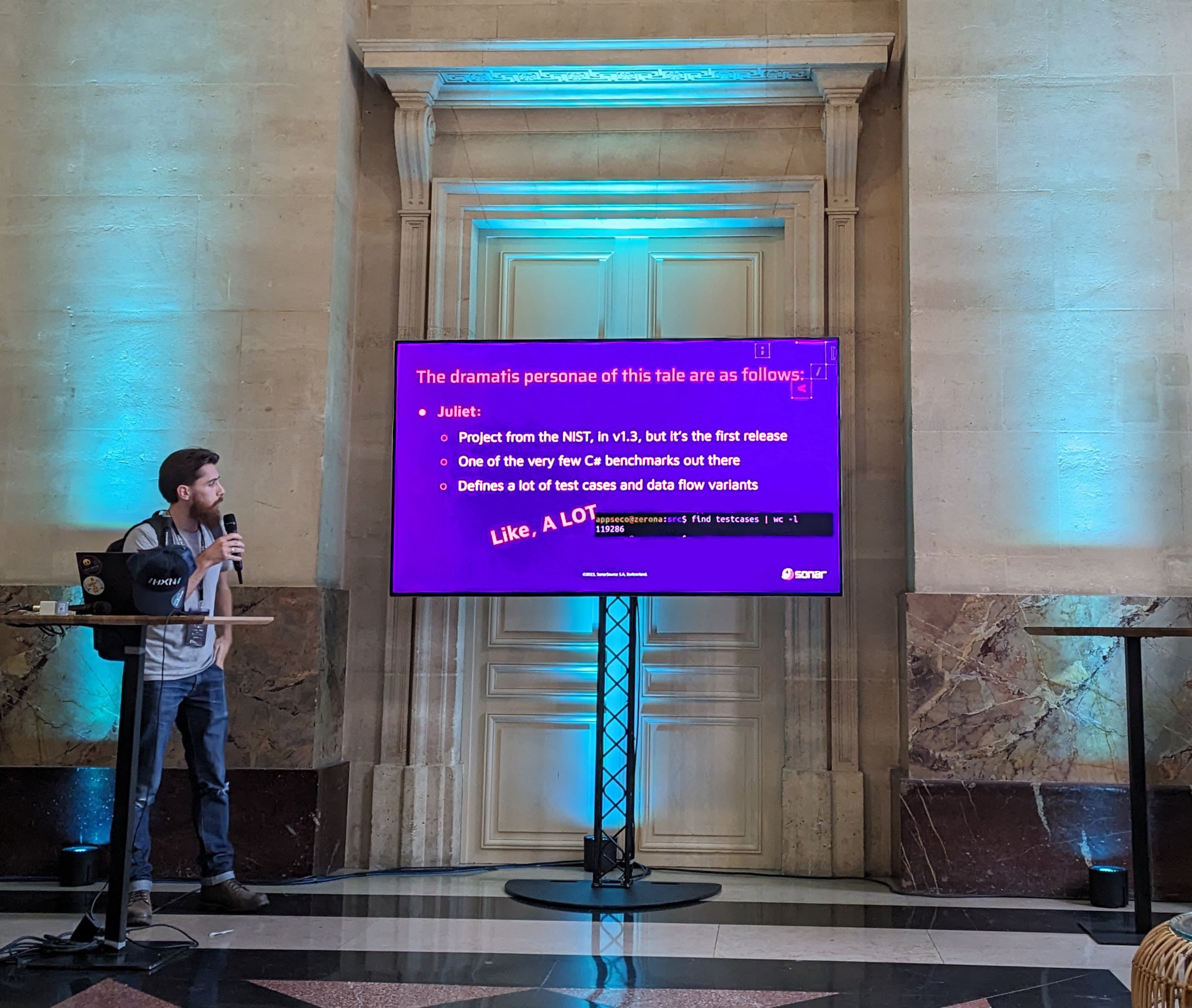
The session describes the challenges faced when improving a SAST engine to cover a specific benchmark. Check out our related blog post Java SAST Benchmarks: why you shouldn’t trust them blindly.
We greatly enjoyed the fresh and diverting lightning talks format and would greatly welcome it to become a regular component of the conference.
Hexacon 2023 - Conclusion
Our expectations after the great conference last year were high. But Hexacon 2023 really smashed it again. We had an amazing time, met a lot of friendly, like-minded people, and enjoyed the cutting-edge content provided by the presented talks.
Kudos to Synacktiv for making this conference such a pleasant event, we are already looking forward to next year for yet another iteration of Hexacon!

https://twitter.com/hexacon_fr/status/1713248413725143356/photo/1

