TL;DR overview
- TyphoonCon 2023 is a Seoul-based offensive security conference where Sonar researchers presented vulnerability research and engaged with the exploit development community.
- Presentations covered advanced exploitation techniques, zero-day discovery workflows, and emerging attack surfaces in widely deployed software.
- The conference provided insights into how security researchers approach vulnerability discovery across different software categories and platforms.
- Sonar's participation at TyphoonCon demonstrates its ongoing investment in original security research that strengthens its static analysis detection capabilities.
Three of our Vulnerability Researchers traveled to Seoul to speak at TyphoonCon 2023, let's look into what happened!

TyphoonCon was created in 2018 by SSD Disclosure and named that way because of the typhoon that hit Hong Kong during the event–future events would later take place in Seoul. They aim to bring security practitioners from around the world to exchange about topics related to vulnerability research, exploitation techniques, reverse engineering, and other topics of the technical security industry.
Aside from the conference, there are also several days of training, an online Capture the Flag competition, and a security contest, TyphoonPwn. The organizers also take great care of their speakers and of the audience, with many organized events for everybody to meet and bond. And let's not forget the sightseeing sessions that gave us a taste of Seoul's beauty.

The talks
Usually, keynotes at technical security conferences tend to cover the same topics so we were pleasantly surprised by Insu Yun’s How to build Skynet – a system that hacks systems and his academic work on how to automatically discover, exploit and mitigate vulnerabilities. Yongil Lee closed the conference with Exploring Offensive Security in Korea, where he gave insights into this industry in South Korea. The country invested a lot in offensive security to thwart new cyber-attacks by investing in research to discover 0-day vulnerabilities before threat actors do.
We then met with Johannes Willbold and Tobias Scharnowski of the Ruhr University Bochum who presented their research on the security of low-orbit satellites in Zero Gravity Exploits: Reverse Engineering and Fuzzing Low-Earth Orbit Satellites. Such devices also suffer from the usual bad security practices of embedded development and they could demonstrate how to take advantage of (simple) memory corruption vulnerabilities to take over satellites from ground stations.
Finally, we had a lot of fun watching When Athletic Abilities Just Aren’t Enough – Scoreboard Hacking by Maxwell Dulin. A very original presentation where Maxwell shows how he could remotely hack a sports scoreboard to change the score, or silently slow down or speed up time.
These presentations gave us important information on the current trends in the industry and will help to improve the security pillar of our Code Quality solution.

"Patches, collisions and root shells: a Pwn2Own Adventure"
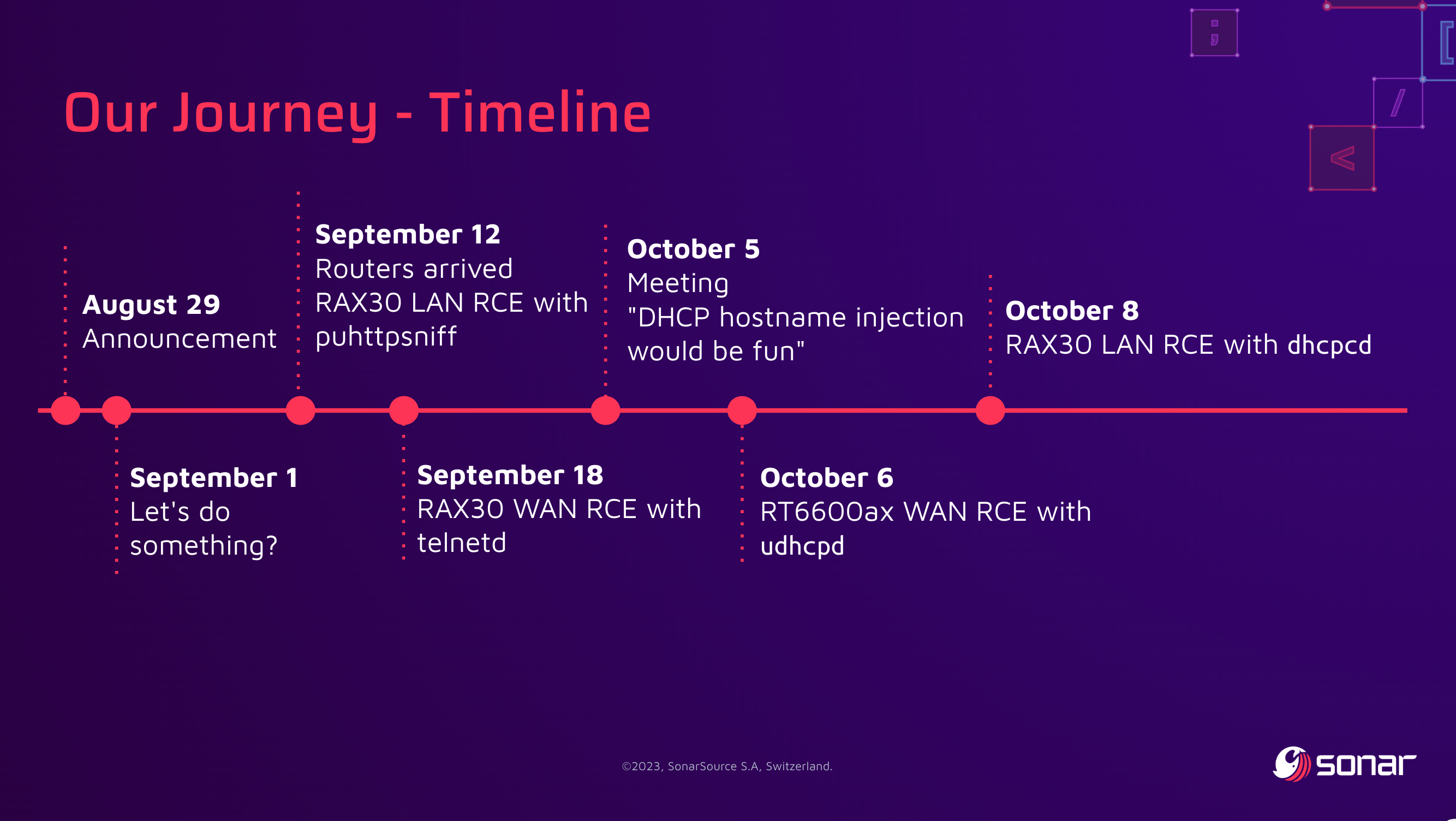
We got to present our talk Patches, collisions and root shells: a Pwn2Own Adventure, showcasing the research that we did for Pwn2Own Toronto. We first came back on how we collaborated together and then on the details of the 4 vulnerabilities that we found, with a live demonstration of one of our exploits on the Synology router.
To prepare for the talk, we also wanted to look into what vulnerabilities we missed and what the others had. This event happened six months ago so many researchers already published their work, and there's a lot to learn from. We published our list on the Wikipedia page of the event, and we encourage all participants to contribute to it!
If you weren't at the conference, stay tuned on August 8, 2023 to read our blog post on all the technical details behind these vulnerabilities.
What's next?
We sure had a great time at TyphoonCon: kudos to the organizers for the great care brought to the event, and everybody else for the presentations and interesting discussions.
Our next big security talk will be at DEF CON 31, in Las Vegas on August 10-13, where we'll present Visual Studio Code is why I have (Workspace) Trust issues. We hope to see you around!


