Sonar's latest blog posts
State of Code Developer Survey report: The current reality of AI coding
Sonar analyzes over 750 billion lines of code every day. This gives us a unique, high-level view of the state of code quality and security across the globe.


Day in the Life: Expanding Sonar into LATAM as a Country Manager
Let's dive in and learn about his drive to expand Sonar's presence in Latin America, what a typical day looks like, and what fuels his passion both in and out of the office.
Read article >
Code Security for Conversational AI: Uncovering a Zip Slip in EDDI
Learn how SonarQube identified a Zip Slip vulnerability (CVE-2025-32779) in EDDI, an open-source conversational AI middleware.
Read article >
Get new blog posts delivered directly to your inbox!
Stay up-to-date with the latest Sonar content. Subscribe now to receive the latest blog articles.
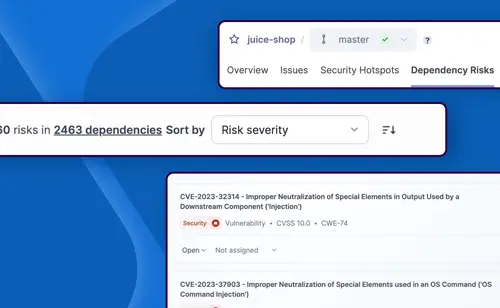
SonarQube Advanced Security now available: developer-first security for all code
Sonar is thrilled to announce a major leap forward: the General Availability (GA) of SonarQube Advanced Security! Building on the foundation trusted by over 7 million developers and 400,000 organizations for industry-leading code quality analysis, SonarQube now delivers the first fully integrated solution for developers to find and fix both code quality and code security issues across their entire codebase.
Read article >

Quality assurance in the AI era: a leadership imperative, according to S&P Global Market Intelligence
In the rapidly evolving AI era, technology leaders are facing a fundamental shift in how code is created, validated, and governed.
Read article >
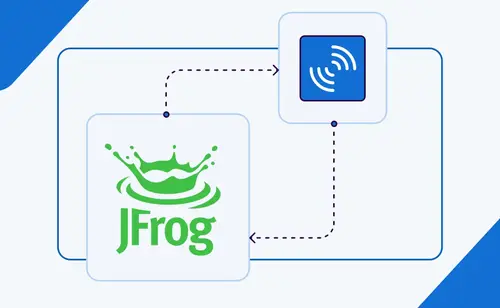
Analysis evidence from SonarQube now available in JFrog AppTrust
By integrating SonarQube's industry-leading automated code review with JFrog's new AppTrust governance platform, together we are providing the essential framework for software engineering teams to embrace AI-driven speed without compromising on control.
Read article >
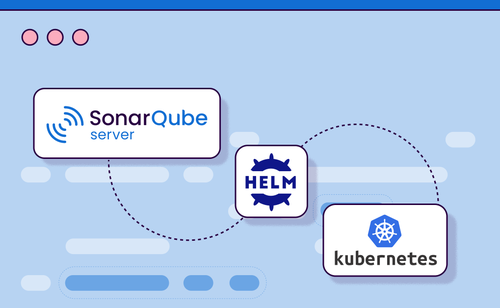
Deploying SonarQube on Kubernetes with Helm Charts
By using a Helm Chart to deploy SonarQube Server, teams can quickly provision a production-ready SonarQube Server instance with minimal configuration while adopting best practices for scalability, security, and maintainability.
Read article >

How reasoning impacts LLM coding models
This report provides a deep dive into GPT-5’s four reasoning modes—minimal, low, medium, and high—to understand the impact of increased reasoning on functional correctness, code quality, security, and cost.
Read article >
Diving into the 3 traits that define your LLM’s coding personality
Our recent “State of code” report moved beyond traditional benchmarks to understand the full mosaic of an LLM's capabilities. The research revealed that while leading models share common strengths and flaws, each has a unique style.
Read article >

The Coding Personalities of Leading LLMs—GPT-5 Update
GPT-5’s arrival on the scene adds an important new dimension to the landscape, so we have updated our analysis to include it.
Read article >
The Coding Personalities of Leading LLMs
Make smarter AI adoption decisions with Sonar's latest report in The State of Code series. Explore the habits, blind spots, and archetypes of the top five LLMs to uncover the critical risks each brings to your codebase.
Read article >
Securing Go Applications With SonarQube: Real-World Examples
Take a deep dive into some vulnerabilities in Go applications and understand how SonarQube Cloud helps developers detect and mitigate them during the development cycle.
Read article >