Start your free trial
Verify all code. Find and fix issues faster with SonarQube.
Get startedTL;DR overview
- SAST (Static Application Security Testing) is a white-box testing method that analyzes application source code for security vulnerabilities without executing it, enabling teams to identify issues early in the development process when they are least expensive to fix.
- Because SAST tools have access to the full codebase, they can scan millions of lines of code using data flow analysis, control flow analysis, and pattern matching—far faster and more thoroughly than manual code reviews.
- Key benefits include early detection of security flaws, automated scanning of large codebases, reduced remediation costs, improved code quality, and support for regulatory compliance requirements.
- SAST integrates with CI/CD pipelines to enforce security checks on every code change, preventing vulnerabilities from reaching production while providing developers with actionable remediation guidance.
What is SAST?
Static Application Security Testing (SAST) is a software testing technique used to identify potential security vulnerabilities in software applications by analyzing the source code of an application without executing the program. SAST is a proactive method for identifying security vulnerabilities and weaknesses before the application is deployed or released to production.
SAST is a vital process of the software development lifecycle (SDLC). It can be used early in the development process when fixing security flaws is more simple and less expensive.
SAST is known as a white-box testing method which means the tool has access to the application's source code. This access enables the tool to conduct a more extensive examination of the code and discover vulnerabilities that a black-box tester would not be able to see.
Why is SAST important?
Security personnel are vastly outnumbered by developers. Obtaining the resources to conduct code reviews on an organization's apps can be difficult. The capability of SAST tools to examine the entire codebase is one of its primary benefits.
The tools are also significantly quicker than human-performed manual secure code reviews by utilizing the potential to scan millions of lines of code automatically with high confidence for security vulnerabilities.
SAST is carried out for a number of significant business factors as an essential part of the application security procedures.
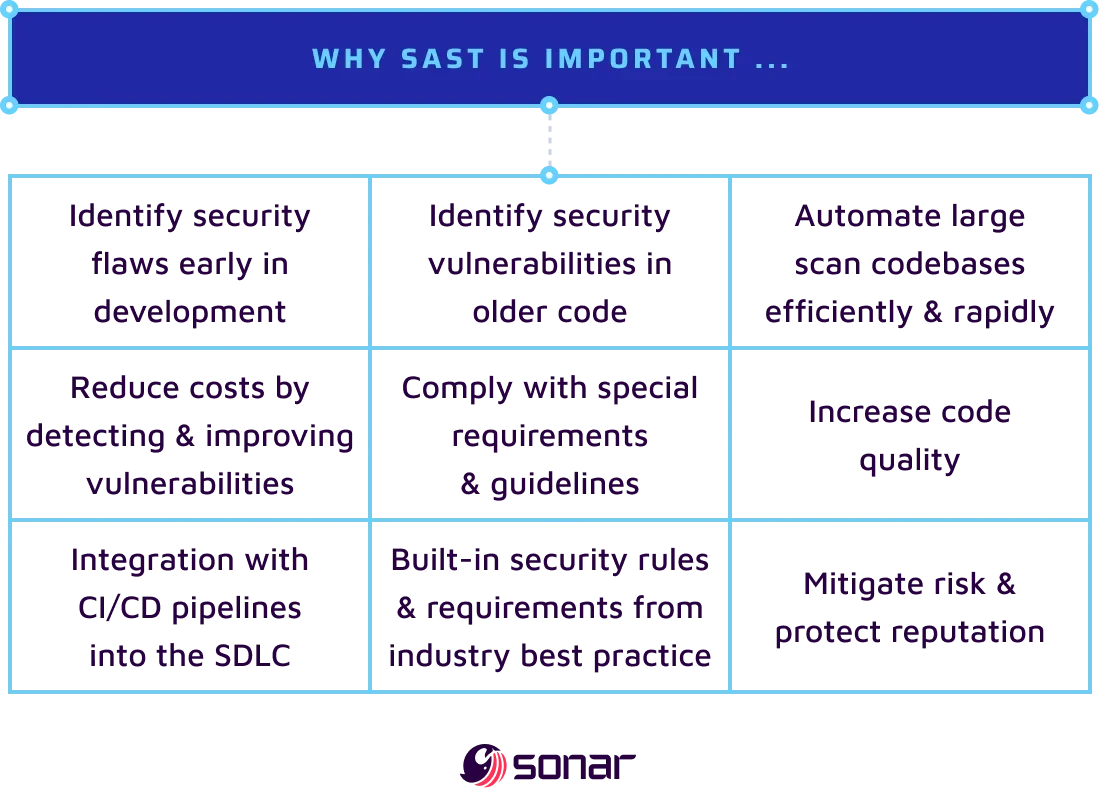
The importance of utilizing SAST includes:
- Identify security flaws at an early stage of development.
- Identify security vulnerabilities in code that is no longer actively being developed.
- Automate large scan codebases efficiently and rapidly.
- Reduce costs by detecting and improving vulnerabilities.
- Comply with special regulatory requirements and guidelines.
- Increase code quality.
- Integration with CI/CD pipelines into the SDLC.
- Build in security rules and requirements from industry best practices.
- Mitigate risk and protect reputation.
SAST and Security
SAST plays a crucial role in ensuring the security of software applications throughout the development workflow and is tightly intertwined in the process of assessing the security of software. SAST contributes to improving application security in various ways.
Employing various techniques like data flow analysis, control flow analysis and pattern matching, SAST can examine a code’s logic, structure and syntax.
SAST tools analyze the detailed codebase to identify potential security vulnerabilities and assist developers and security teams to understand the potential risk and remediation priorities. Input validation errors, buffer overflows, cross-site scripting (XSS), injection attacks (such as SQL injection and command injection), unsafe cryptographic implementations, authentication and authorization problems, and security configuration errors are a few examples.
SAST solutions help businesses comply with legal and regulatory standards. Many different industries have their own security requirements, such as PCI DSS, HIPAA, or GDPR. SAST assists in locating vulnerabilities at the code level that might breach these requirements. Organizations can assure compliance and reduce the potential of fines or legal repercussions by proactively addressing these concerns.
SAST encourages developers to use secure coding practices by evaluating the codebase and offer feedback and suggestions on possible security flaws. Developers can utilize this knowledge to strengthen their coding procedures, follow security best practices, and stay clear of mistakes that frequently result in vulnerabilities. SAST serves as a teaching and training tool that improves developers' understanding of and proficiency with secure coding.
SAST makes it possible for the early detection of security flaws during the development phase. Organizations may detect vulnerabilities early by examining the code before it goes to deployment, decreasing the likelihood of breaches in production. Early vulnerability identification and repair reduce the amount of time, resources, and potential financial losses brought on by security breaches.
SAST can be easily included in the software development workflow fitting into CI/CD pipelines and ensuring the integration of security analysis continuously and consistently throughout the SDLC. By using SAST to automate the security review process, organizations are able to conduct security audits and minimize the risk of security vulnerabilities passing through to production from human error or neglect.
SAST helps to increase overall code quality while concentrating on security weaknesses. SAST tools analyze the codebase to find coding flaws, potential performance problems, and violations of coding standards. This results in applications that are easier to maintain, reliable, portable and much more secure overall.
By proactively detecting and correcting security weaknesses, SAST helps to reduce risk and protects organizational reputation. Early vulnerability mitigation helps firms lower their risk of security threats, data breaches, and the resulting financial and reputational harm. Maintaining consumer trust, preserving the organization's reputation, and avoiding any legal and regulatory problems are all facilitated by ensuring application security with SAST.
SAST and Scanning
Scanning is an essential component of the SAST process involving the use of specialized tools and techniques to methodically analyze the code of software applications in order to find security vulnerabilities and weaknesses.
SAST employs several scanning techniques to inspect the codebase for security vulnerabilities including:
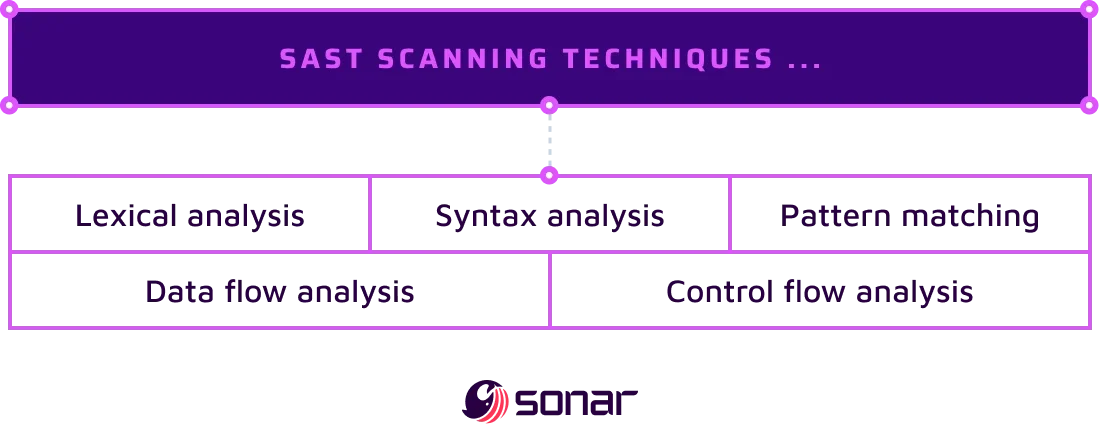
Lexical Analysis
In order to discover variables, functions, and control flow components, this technique parses the code and examines the lexical structure.
Syntax Analysis
Where the code is checked for syntactic correctness to make sure it follows the programming language's standards.
Data Flow Analysis
Monitors the data flow within the code to find any potential security flaws that can result from incorrect data handling, like tainted input or unsafe data flows.
Control Flow Analysis
Analyzes the control flow of the code, monitoring the progress of execution to find possible vulnerabilities caused by careless handling of conditions, loops, or function calls.
Pattern Matching
This technique looks for certain coding patterns that indicate the presence of security flaws, such as unreliable cryptographic algorithms or potential injection attacks, using predetermined patterns or regular expressions.
When scanning code with SAST, false positives may be created. SAST tools commonly come with features for filtering and prioritizing findings that can assist in reducing false positives. This assists in directing developers and security teams toward actual security issues.
SAST scanning can generate extensive reports with in-depth analyses of the discovered security vulnerabilities. Reports normally encompass of summary of the results, a list of vulnerabilities found, descriptions, severity ratings and remedial suggestions. Developers and security teams can use these reports as informative resources to set priorities and deal with the concerns that have been found.
SAST scanning can be incorporated into the software development lifecycle (SDLC) and development environments to enable automatic security scanning. It may be implemented in code repositories, integrated development environments (IDEs), or continuous integration/continuous delivery (CI/CD) pipelines. These integrations assures security scanning is executed frequently and consistently during the development process.
SAST Tools
SAST tools are applications used to examine software application's source code for potential security flaws; scan the codebase, enforce security rules, and find potential security problems, these tools use a variety of methodologies.
SAST tools are effective resources for finding security flaws in software programs as they are being developed, promoting secure coding techniques, and boosting their overall security. They help developers proactively address potential security vulnerabilities by automating code analysis and giving them useful information.
Some of the leading SAST tools in the market include SonarQube Server, SonarQube Cloud, Veracode, Codacy, and Checkmarx.
Sonar's industry-leading Code Quality solution offers automated code review and comprehensive static code analysis capabilities. Designed to detect and fix a wide range of code quality issues, bugs, and security vulnerabilities, Sonar supports over 30 programming languages and frameworks.
With a true shift left approach starting from the IDE with SonarQube for IDE and through the stages of the DevSecOps workflow with SonarQube Server and SonarQube Cloud, developers and security champions can ensure the security and reliability of their codebase.
