TL;DR overview
- SonarQube integrates with GitHub Code Scanning via SARIF output, enabling SonarQube analysis results to appear directly in the GitHub Security tab and on pull requests alongside native GitHub security findings.
- The integration allows teams to use SonarQube's deeper SAST engine—including interprocedural taint analysis—while surfacing results in GitHub's native security interface, reducing tool-switching friction for developers.
- Security vulnerabilities flagged by SonarQube through GitHub Code Scanning appear in the same pull request workflow as GitHub's own alerts, making it easier for developers to see and act on findings without leaving their existing review process.
- Teams using GitHub Advanced Security can enable SonarQube SARIF upload as part of their CI pipeline with minimal configuration, layering SonarQube's broader vulnerability detection on top of GitHub's native scanning.
Today, for GitHub repositories, our SAST analysis provides fast, precise security feedback directly inside your pull requests.
You instantly know how many vulnerabilities are detected and, until now, you would systematically go to SonarQube Cloud to start investigating.
Not anymore.
From this point forward, developers can review the list of vulnerabilities from GitHub’s interface, thanks to code scanning.
We’re happy to announce that SonarQube Cloud integrates with GitHub code scanning!
It’s available to everyone with a GitHub repository - private or public - independently of your SonarQube Cloud plan.
If you have access to the feature on GitHub and your organization admin already accepted the update for the SonarQube Cloud app permissions, you’re all set!
You should be able to start using the feature during your next code review.
GitHub Code Scanning Introduction
As GitHub describes it, code scanning is a developer-first, GitHub-native approach to easily find security vulnerabilities before they reach production.
GitHub code scanning helps you review and prioritize vulnerabilities during your code review process, in your development workflow.
You don’t systematically have to switch context for your reviews anymore. How convenient!
GitHub Code scanning is free for public projects or available as a paid option for your private repos with GitHub's Advanced Security package.
The feature is also available in GitHub Enterprise.
To access the code scanning alerts, you have two options:
- At the repository level, click on the ‘Security’ tab, and ‘View alerts’.
- In your pull request, click on the ‘Checks’ tab, ‘Code scanning results’, and ‘SonarQube Cloud’
3 reasons to start using GitHub code scanning with SonarQube Cloud
1. Easy code security review & prioritization
With GitHub code scanning alerts, we’re making your code security review easier. From now on, in the event of a failed quality gate for instance, you can easily review the full list of security vulnerabilities in the pull request, and start prioritizing your work in GitHub.
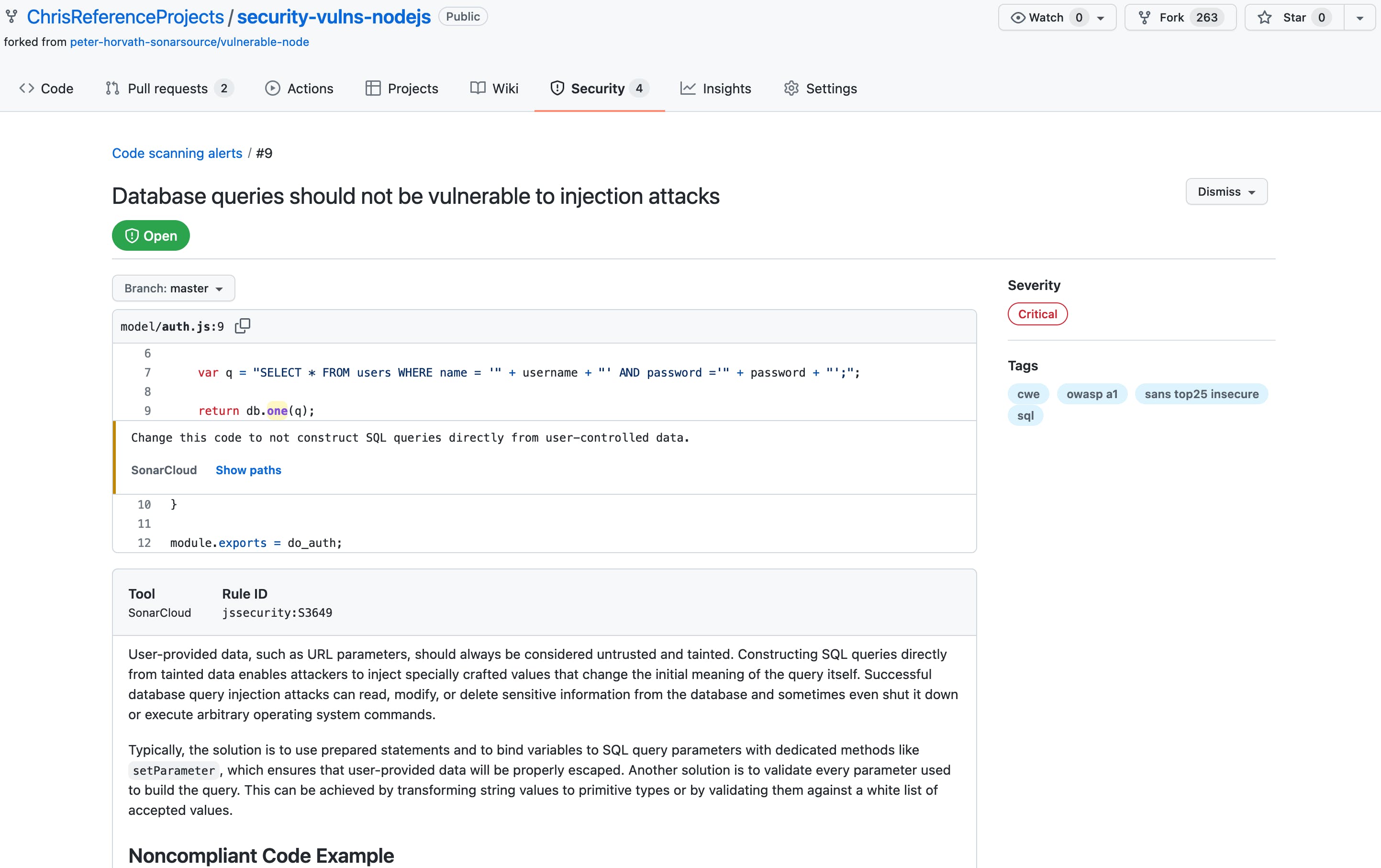
2. Fast code security vulnerability investigation
GitHub code scanning, together with SonarQube Cloud analysis, provides everything you need to investigate a vulnerability.
Directly in GitHub, you can learn why you have an issue, where it’s located and how it flows in your code.
To help you with that, you’ll find the full rule description along with a relevant example of a compliant implementation.
3. Instant issue status synchronization
More than just a security review, code scanning will also allow you to dismiss vulnerabilities that you think are False Positives, or something you Won’t Fix.
Two clicks are all it takes.
When you do, SonarQube Cloud will automatically be synchronized and your PR decoration refreshed instantly.
In the same way, if you update a vulnerability status in SonarQube Cloud, GitHub code scanning will be updated to reflect the latest changes.
So whatever status update, the two environments will always be aligned.
Better code scanning security oversight
Give it a try during your next code review, and share your experience in our community forum.
With GitHub code scanning and SonarQube Cloud static analysis, you have all you need to catch security vulnerabilities before they make their way to production!
For more information, please check our documentation for GitHub code scanning alerts.