TL;DR overview
- A SQL injection vulnerability in Joomla allows attackers to escalate privileges by injecting malicious SQL into user group or role management queries, bypassing access controls.
- The flaw is exploitable by low-privilege authenticated users, enabling them to grant themselves administrative access without knowing the admin password.
- Joomla's use of an ORM does not prevent this vulnerability because the injection point bypasses parameterized queries through dynamic query construction in an affected component.
- Joomla administrators should apply the patch, review recent user account changes for signs of exploitation, and consider enabling multi-factor authentication for all admin accounts.
Joomla! is one of the biggest players in the market of content management systems and the second most used CMS on the web. We discovered a second-order SQL injection (CVE-2018-6376) that could be used by attackers to leverage lower permissions and to escalate them into full admin permissions on Joomla! prior version 3.8.4.
Who is affected
Installations with the following requirements are affected by this vulnerability:
- Joomla! version <= 3.8.3 and >= 3.7.0
For exploitation, an attacker needs to be authenticated to the Joomla! backend with a Manager account. This user group is available by default in Joomla! and has lower privileges than the Administrator or Super Users user groups.
Impact - What can an attacker do
An attacker exploiting this vulnerability can read arbitrary data from the database. This data can be used to further extend the permissions of the attacker. By gaining full administrative privileges she can take over the Joomla! installation by executing arbitrary PHP code.
In this blog post we will demonstrate how the RIPS static code analyzer was used to automatically find the previously unknown vulnerability. Further, we discuss the technical details behind the security issue.
Technical Analysis: Second-Order Blind SQL Injection
The SQL injection is located in the file administrator/templates/hathor/postinstall/hathormessage.php. The following code summary shows the vulnerability.
administrator/templates/hathor/postinstall/hathormessage.php
1 function hathormessage_postinstall_condition()
2 {
3 ⋮
4 $adminstyle = $user->getParam('admin_style', '');
5 if ($adminstyle != '')
6 {
7 $query = $db->getQuery(true)
8 ->select('template')
9 ->from($db->quoteName('#__template_styles'))
10 ->where($db->quoteName('id') . ' = ' . $adminstyle[0])
11 ->where($db->quoteName('client_id') . ' = 1');
12
13 // Get the template name associated to the admin style
14 $template = $db->setquery($query)->loadResult();
15 ⋮
16 }
17 ⋮
18 }The function hathormessage_postinstall_condition() is called by a component for post-installation messages introduced in Joomla! 3.2.0 every time the dashboard is loaded. In this function, the content of the variable $adminstyle gets concatenated into the WHERE part of the constructed SQL query without proper sanitization in line 10. If an attacker can control the content of the parameter admin_style, she can inject arbitrary SQL into the query that is executed in line 14.
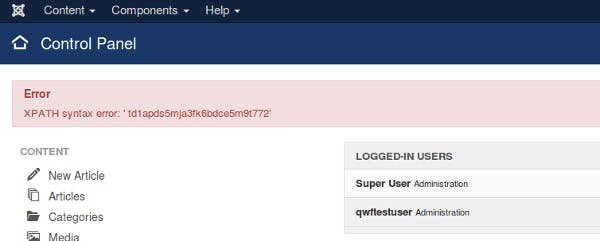
The parameter admin_style is received in line 4. It contains the ID of the backend template that the user has configured for usage. A user can change this parameter in his profile settings. A quick verification by intercepting the saving request for user parameters and changing the value for admin_style showed that it is saved to the database without any further check or sanitization. Thus, an attacker can inject arbitrary content into this parameter that is later used in the SQL query. This SQL injection is a second-order vulnerability since the payload is first saved to the database and later used in the query. The query result is not displayed directly on the web page, thus, an attacker needs to use error-based or timing-based injection techniques for exploitation. The following figure demonstrates how an XPath error message within the SQL query can be used to read out the session ID of a currently logged-in administrator.
Timeline
Summary
Security vulnerabilities are everywhere and can be found even in the most popular and most reviewed open source applications. A new SQL injection vulnerability was uncovered in Joomla! that affects versions prior to 3.8.4. In this blog post, we examined the roots of the second-order blind SQL injection and demonstrated how static analysis can help finding such hidden security issues in large and complex PHP projects.
We would like to thank the security team behind Joomla! for their professional collaboration and for quickly resolving the issues with the release of version 3.8.4. If you are still using an older version, we encourage you to update.
Related Posts
- Exploiting Hibernate Injections
- Joomla! 3.7.5 - Takeover in 20 Seconds with LDAP Injection
- Backend SQL Injection in BigTree CMS 4.4.6
- dotCMS 5.1.5: Exploiting H2 SQL injection to RCE
- CubeCart 6.1.12 - Admin Authentication Bypass
- Pre-Auth Takeover of OXID eShops
- Breaking Into Your Company's Internal Network - SuiteCRM 7.11.4