Sonar's latest blog posts
State of Code Developer Survey report: The current reality of AI coding
Sonar analyzes over 750 billion lines of code every day. This gives us a unique, high-level view of the state of code quality and security across the globe.


Regular expressions present challenges even for not-so-regular developers
Regular expressions are a concise and powerful tool for processing text. However, they also come with a steep learning curve and plenty of opportunities to make mistakes. This is the first in a series of posts about some specific regex pitfalls.
Read Blog >

What I learned from the Server Side Public License
When the Server Side Public License (SSPL) was submitted to the Open Source Initiative (OSI), many people criticized it, and the license was eventually withdrawn.
Read article >
Get new blog posts delivered directly to your inbox!
Stay up-to-date with the latest Sonar content. Subscribe now to receive the latest blog articles.

Code security: now there's a tool for developers
Hey SonarQube Server and SonarQube Cloud users! You now have a tool to own Code Security! SonarSource has been hard at work for the last year to give you the tooling to review and improve your code security. We're glad to say that today you have at your fingertips unmatched precision and performance in SAST (Static Application Security Testing) analysis for five languages and counting.
Read Blog >

Code Security Advent Calendar 2020
It's time to have some December fun! We have 24 little challenge gifts awaiting you that hide security vulnerabilities in real-world Java, C#, PHP and Python code. Can you spot the vulnerability?
Read Blog >

Make Code Quality & Security™ an integral part of your workflow
SonarQube Server Developer Edition overlays Code Quality and Security™ right onto your projects. Your pull requests are automatically analyzed and decorated with a clear Go/No Go Quality Gate so you only merge clean, quality code! 👏
Read Blog >

How SonarQube Cloud finds bugs in high-quality Python projects
As developers, there always comes a time when we find a bug in production and wonder how it passed all our quality checks. Let's go over a few Bugs we found with SonarQube Cloud and see why it is able to detect them when popular linters don't .
Read Blog >

Code vulnerabilities put health records at risk
Recently, we discovered several code vulnerabilities in OpenEMR 5.0.2.1. A combination of these vulnerabilities allowed remote attackers to execute arbitrary system commands on any OpenEMR server that uses the Patient Portal component. This can lead to the compromise of sensitive patient data, or worse, to a compromise of critical infrastructure.
Read Blog >

Winning the race against TOCTOU vulnerabilities in C & C++
Security is an eternal race between the techniques and technologies of attackers and those of the defenders. Today, I'm proud to announce a step forward for defenders with a new rule to detect a literal race condition: TOCTOU (or TOCTTOU) vulnerabilities, known in long-form as Time Of Check (to) Time Of Use.
Read Blog >
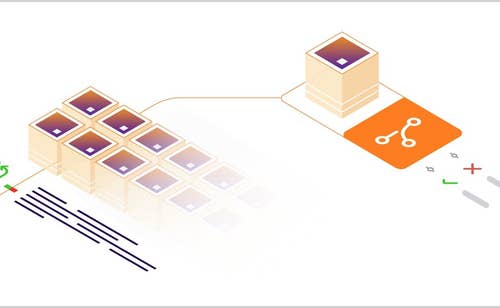
Mono-repository support for GitHub and Azure DevOps Services available now!
Take a tour of SonarQube Cloud's integration with mono-repositories in GitHub and Azure DevOps Services. This new feature allows you to define multiple Quality Gates per project and receive multiple results in your pull requests.
Read Blog >
Pandora FMS 742: Critical Code Vulnerabilities Explained
How code vulnerabilities in your web application can be the single point of failure for your IT infrastructure’s security.
Read Blog >
False positives are our enemies, but may still be your friends
When writing a rule for static analysis, it’s possible that in some cases, the rule does not give the results that were expected. Unfortunately, naming a false positive is often far easier than fixing it. Learn how the different types of rules give rise to different types of false positives, which ones are easier to fix than others, and how you can help.
Read Blog >