Sonar's latest blog posts
State of Code Developer Survey report: The current reality of AI coding
Sonar analyzes over 750 billion lines of code every day. This gives us a unique, high-level view of the state of code quality and security across the globe.


SmartStoreNET - Malicious Message leading to E-Commerce Takeover
Check out the details of a Cross-Site Scripting bug in the BBCode processing in SmartStoreNET and how it can be chained into arbitrary code execution!
Read Blog >

Agent 007: Pre-Auth Takeover of Build Pipelines in GoCD
We recently discovered critical security issues in the popular CI/CD solution GoCD that can be exploited by unauthenticated attackers
Read Blog >
Get new blog posts delivered directly to your inbox!
Stay up-to-date with the latest Sonar content. Subscribe now to receive the latest blog articles.

Meet the new project experience for SonarQube Cloud
We are very pleased to announce that we have released a new project experience. It’s now available in SonarQube Cloud for all users. You’ll notice a few improvements the next time you open SonarQube Cloud.
Read Blog >

Squirrel Sandbox Escape allows Code Execution in Games and Cloud Services
We discovered and reported a vulnerability in the Squirrel VM, written in C, that allows an attacker to escape the sandbox.
Read Blog >

Supercharge your C++ analysis with SonarQube for IDE for CLion
This article talks about the powerful capabilities of the C++ analyzer with SonarQube for IDE and highlights some unique and interesting quality and security rules you might find useful. Through that lens, we demonstrate how you can leverage these rules to elevate your CLion built-in static analysis capabilities for your C++ projects.
Read Blog >

Modernize Code Quality with ‘Quick Fixes’
Boost your productivity by automatically applying fixes to repair code quality issues in your IDE with SonarQube for IDE.
Read Blog >
Cachet 2.4: Code Execution via Laravel Configuration Injection
We responsibly disclosed three vulnerabilities in the open-source status page Cachet, allowing attackers to take over instances. Here are all the details!
Read Blog >
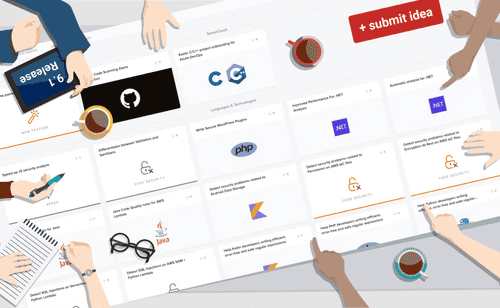
Product portals open: we want your input
We've recently opened up product portals on Productboard. You'll find them for SonarQube Server, SonarQube Cloud, and SonarQube for IDE. Each one shows the features we're currently working on, the ones we've released recently, and the ones we're planning.
Read Blog >

Ghost CMS 4.3.2 - Cross-Origin Admin Takeover
We recently discovered an XSS vulnerability in the admin frontend of Ghost CMS 4.3.2. Find out the details and learn how to avoid such issues in your code!
Read Blog >
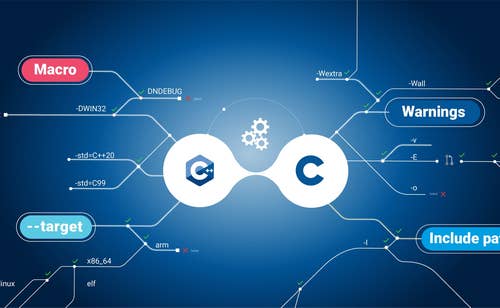
Compilation database: An alternative way to configure your C or C++ analysis
Analyzing your C or C++ code requires, in addition to the source code, the configuration that is used to build the code. Historically we have provided a tool to automate the extraction of this information, called the build wrapper. Recently we introduced another way to configure your analysis, the compilation database. Learn more about the pros and cons of each option.
Read Blog >

elFinder - A Case Study of Web File Manager Vulnerabilities
Our case study of elFinder 2.1.57 describes several critical code vulnerabilities commonly found in web file managers and how to patch them.
Read Blog >