Build and create on Clean Code Foundations
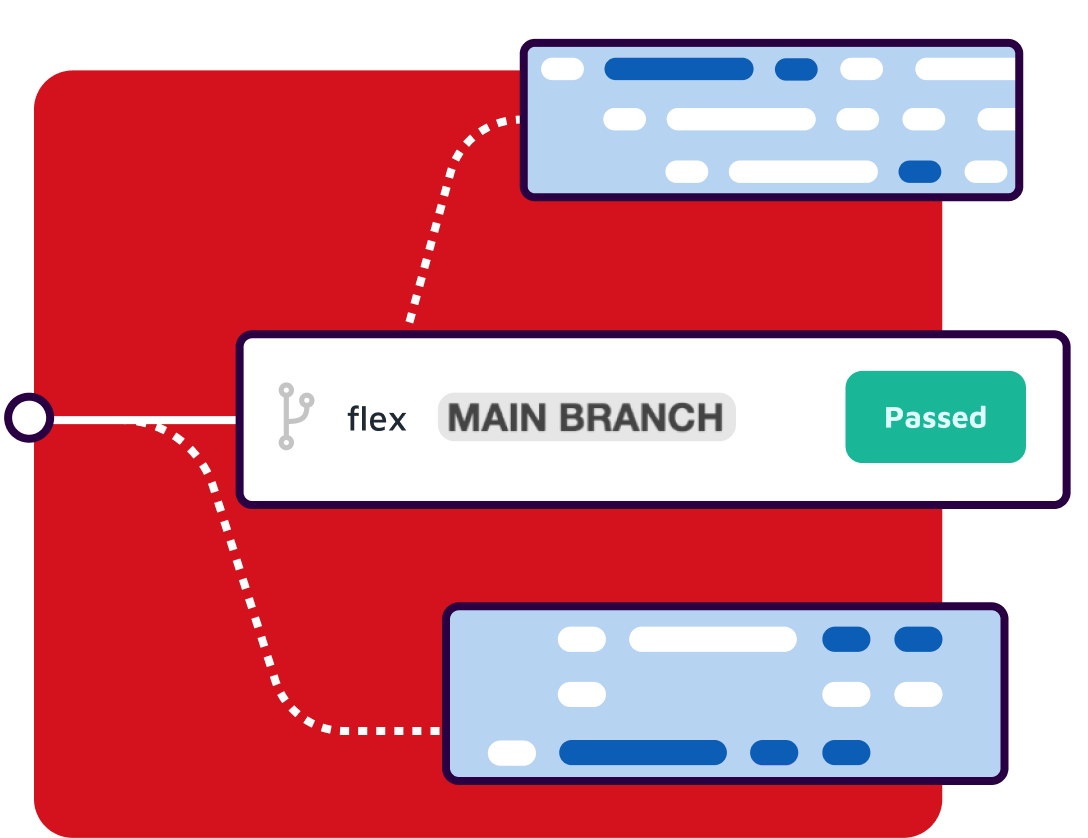
Sonar static code analysis helps you build secure, maintainable, high-quality C software. Covering popular build systems, standards, and versions, Sonar elevates your coding standards while keeping dangerous security vulnerabilities at bay.