One integrated platform for all your code

Actionable code intelligence
SonarQube is the only integrated code quality and code security platform that delivers actionable code intelligence for first-party code, AI-generated code, and open source code—all in a single, integrated solution. No matter the source, you get a holistic view of your code’s health and security.

All-in-one code security analysis
SonarQube delivers an integrated solution for code quality, SAST, taint analysis, SCA, secrets detection, and IaC scanning. It provides comprehensive insights into bugs, vulnerabilities, CVEs, SBOMs, and licenses, streamlining your workflow and eliminating tool sprawl.

Developer-centric workflow
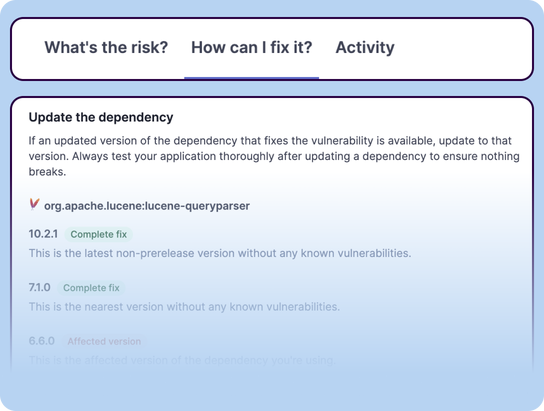
See open source vulnerabilities and license issues directly in your PRs, CI/CD, and soon IDE. This direct feedback minimizes context switching, speeds up fixes, ensures secure dependencies, and clear risk policies keep your development pipeline unblocked.

Security compliance reports
Review the trend and severity of your security issues across single projects or entire application portfolios and generate compliance reports for industry standards such as PCI DSS, OWASP Top 10, CWE, STIG, and more. Scheduled reports allow convenient daily, weekly, or monthly delivery.
Ecosystem support
世界中の700万人以上の開発者に信頼されています












The challenge
Today's rapid development, AI code, and open source reliance are amplifying complex security risks that customers urgently need to minimize.
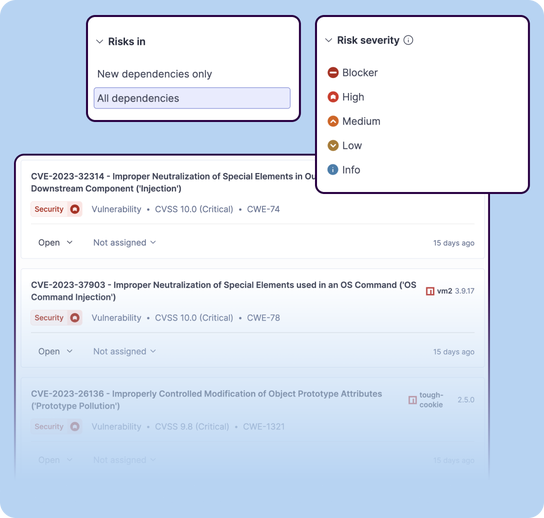
Security vulnerabilities
Vulnerabilities in open source dependencies expose applications to attacks. Ignoring production usage of open source packages can lead to breaches and disruptions. Attackers often weaponize disclosed vulnerabilities quickly, shrinking your remediation window. Without clear visibility and prioritization, teams drown in noisy alerts and unintentionally ship risk to production.
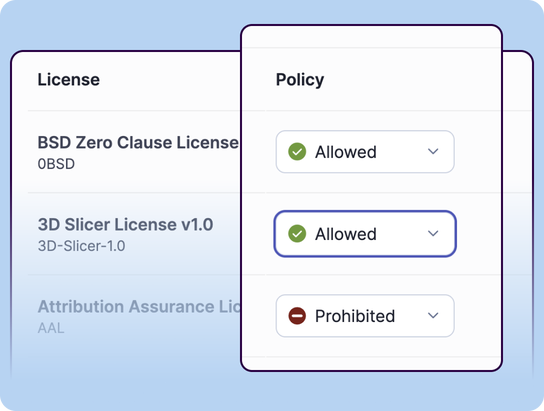
License violations
Incompatible licenses create legal, compliance, and business risks. Automated license policies and enforcement in PRs and CI/CD surface prohibited or risky licenses early, before they reach production.
Supply chain security
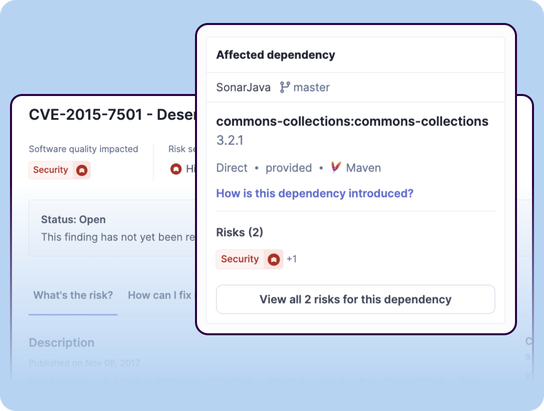
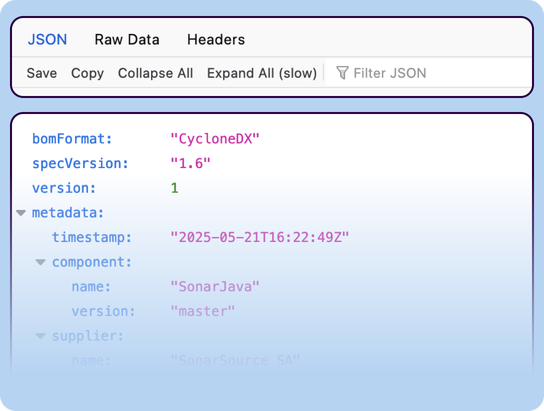
Your applications are built on a complex web of open source dependencies. How can you be sure their maintainers prioritize and follow secure software development practices? This lack of visibility creates significant risk in your supply chain. Transitive dependencies obscure provenance and risk paths. SBOMs and dependency graphs restore visibility and guide focused remediation.
Developer toil and fatigue
Chasing endless security alerts steals developer time from building features. Having to keep track of new security reports, how and where transitive packages came into the application, and managing the lifecycle of non-urgent vulnerabilities significantly amplifies this wasted effort and developer frustration. Automated triage that prioritizes exploitable risks and suppresses noise keeps developers focused on shipping value.
SonarQube SCAがどのように解決するか
SonarQube SCAは開発者向けに構築されており、シームレスで、実用的で、統合されています。
ライセンスチェック
禁止または許可されているソフトウェアライセンスの事前定義セットから選択するか、独自のポリシーを定義します。自動チェックにより、互換性のないライセンスやリスクのあるライセンスが問題になる前に検出されます。
メンテナネットワーク
Sonar は、オープンソース プロジェクトのメンテナーに報酬を支払い、安全なソフトウェア開発手法の遵守と文書化、独自の洞察の提供を求める積極的なアプローチを採用しています。